FRTB Capital Governance
Edition 2026.05
Capital figures your audit, model‑risk, and regulator can replay, line by line.
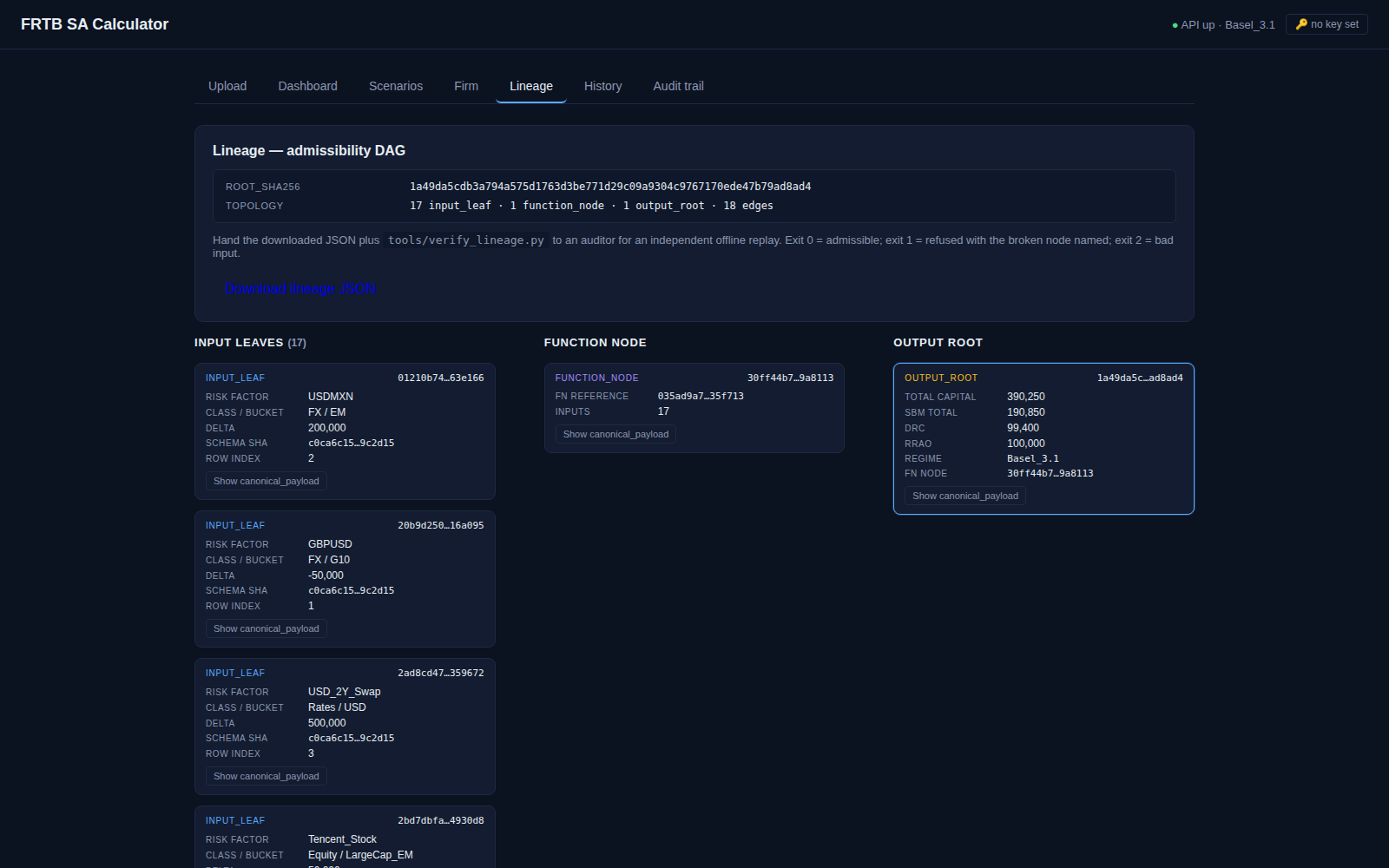
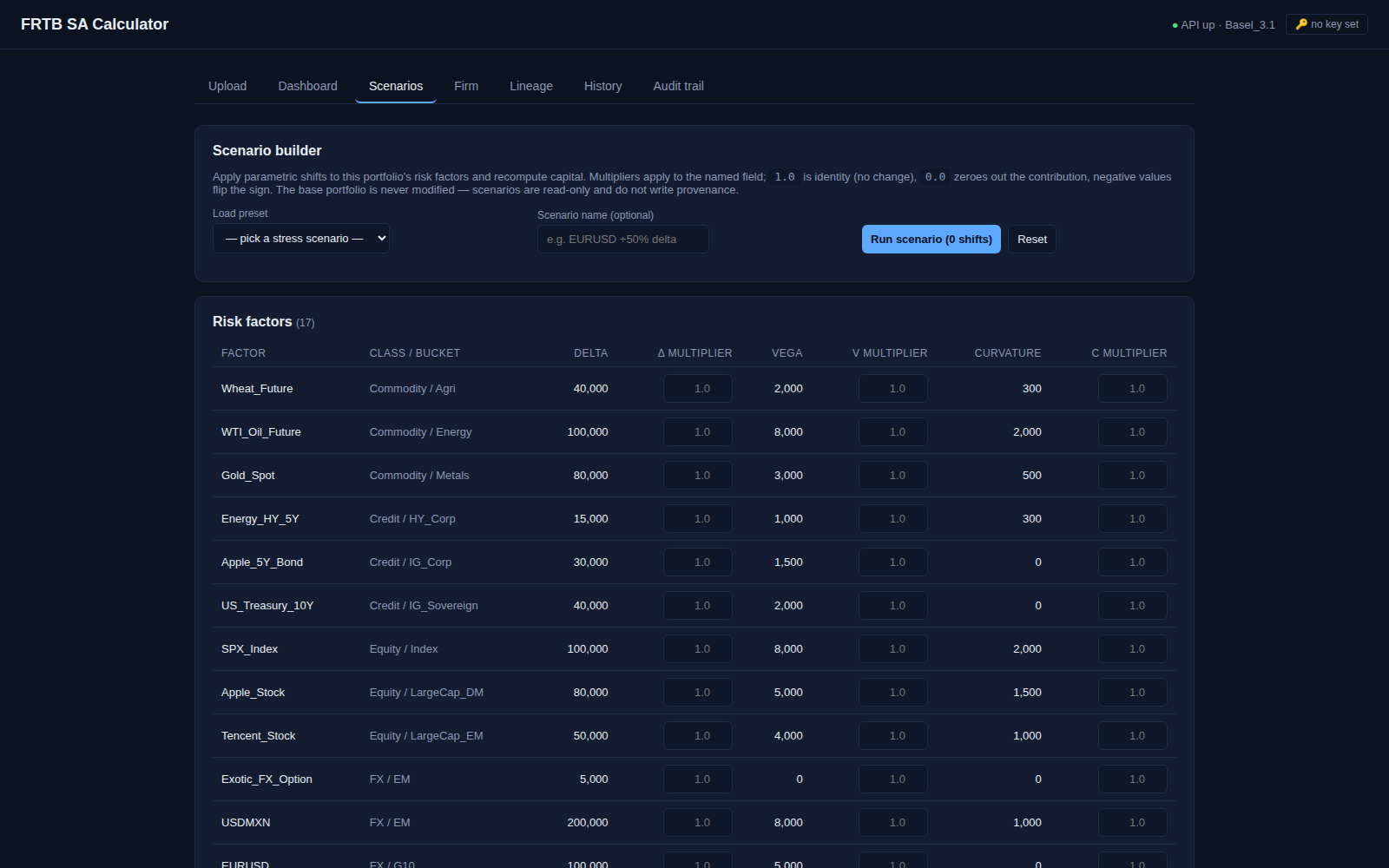
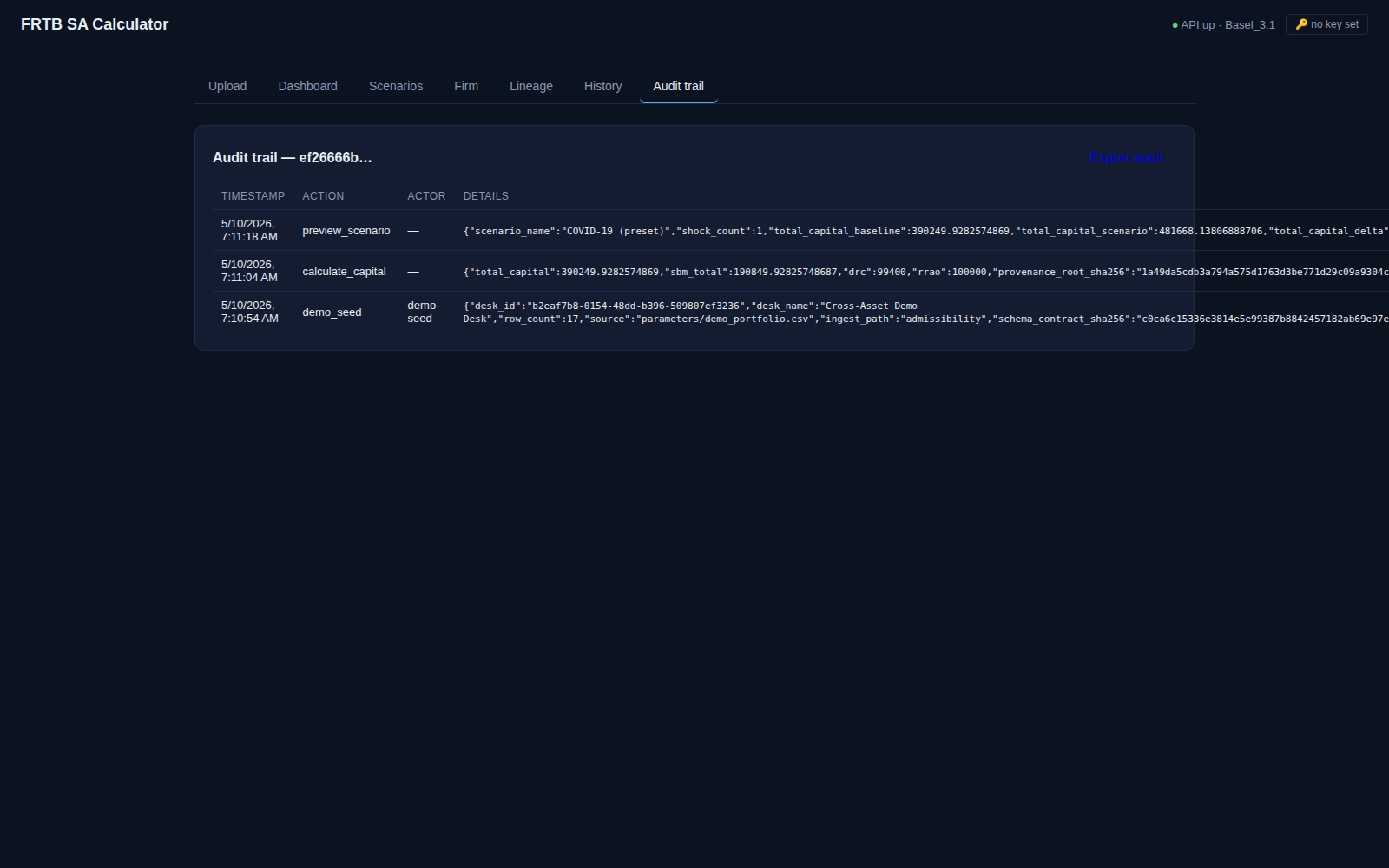
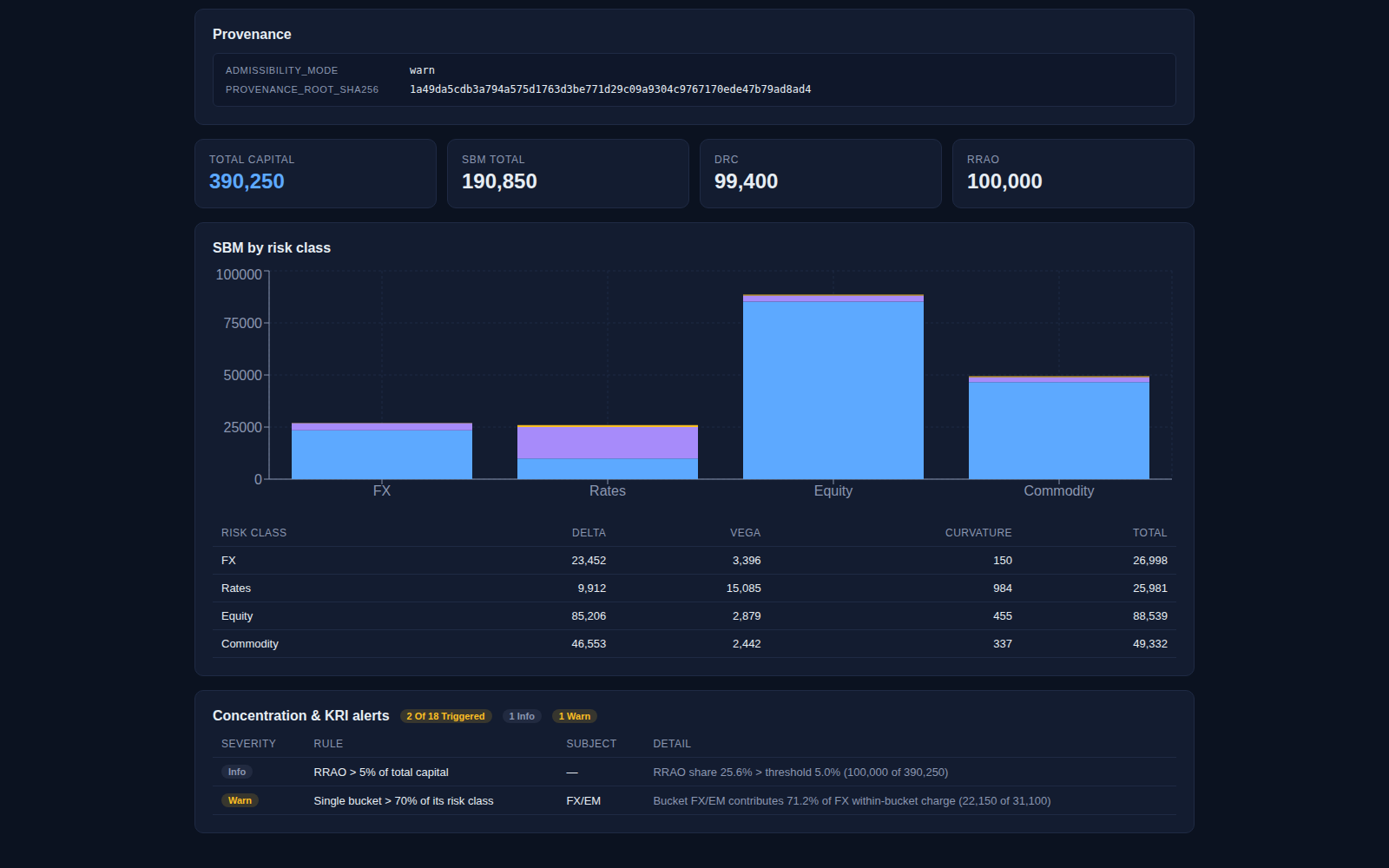
A self-hosted FRTB calculator where every number is a node in a Merkle DAG anchored to its inputs and to the function identity that produced it. Drift any of those — input bytes, schema contract, engine version, regime parameters — and the verifier identifies the exact node where the chain breaks.
Institutional infrastructure, not a self-serve product. Access granted after a brief conversation. Marketing pages, doctrine, roadmap, and verifier explainer are public.
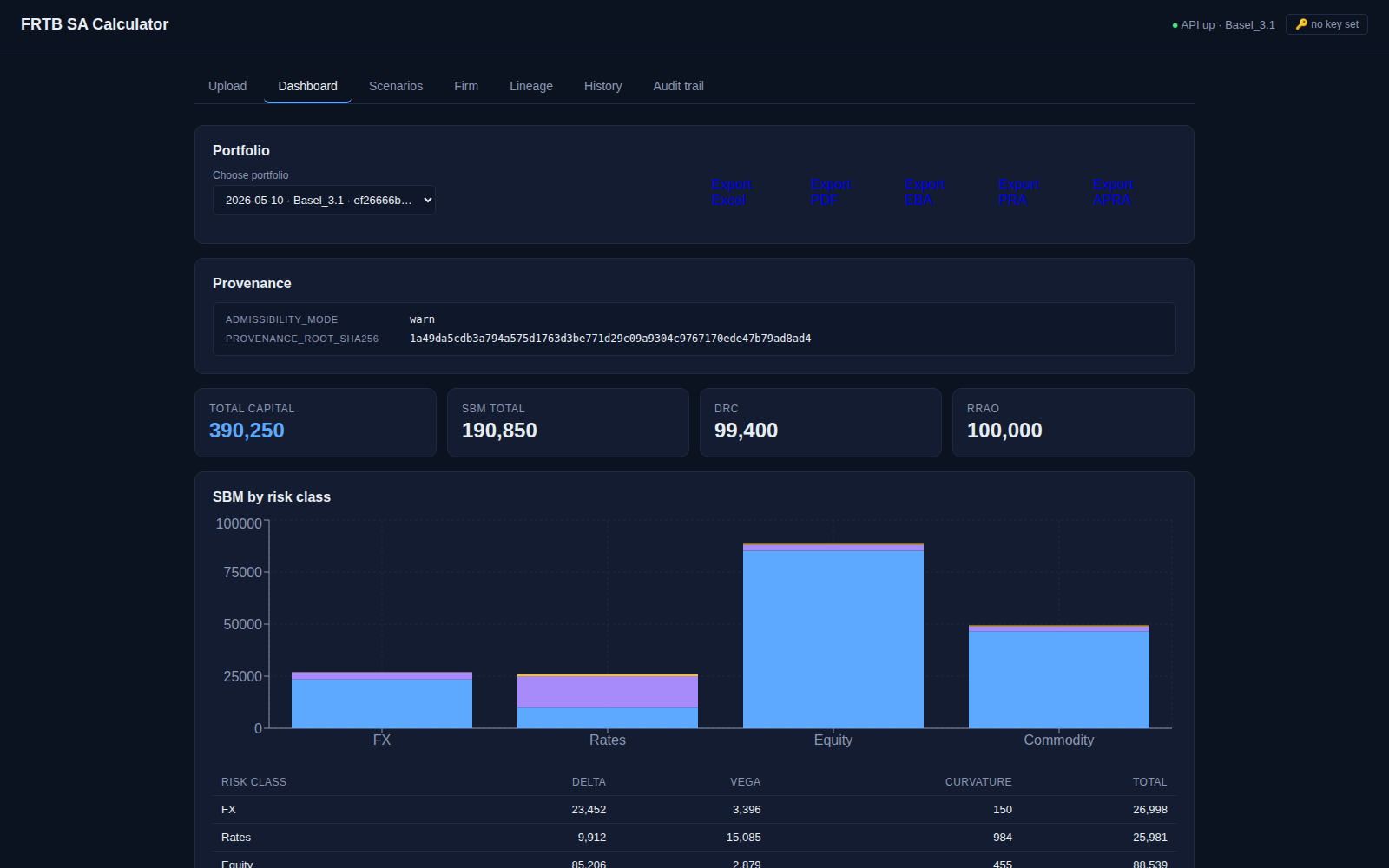
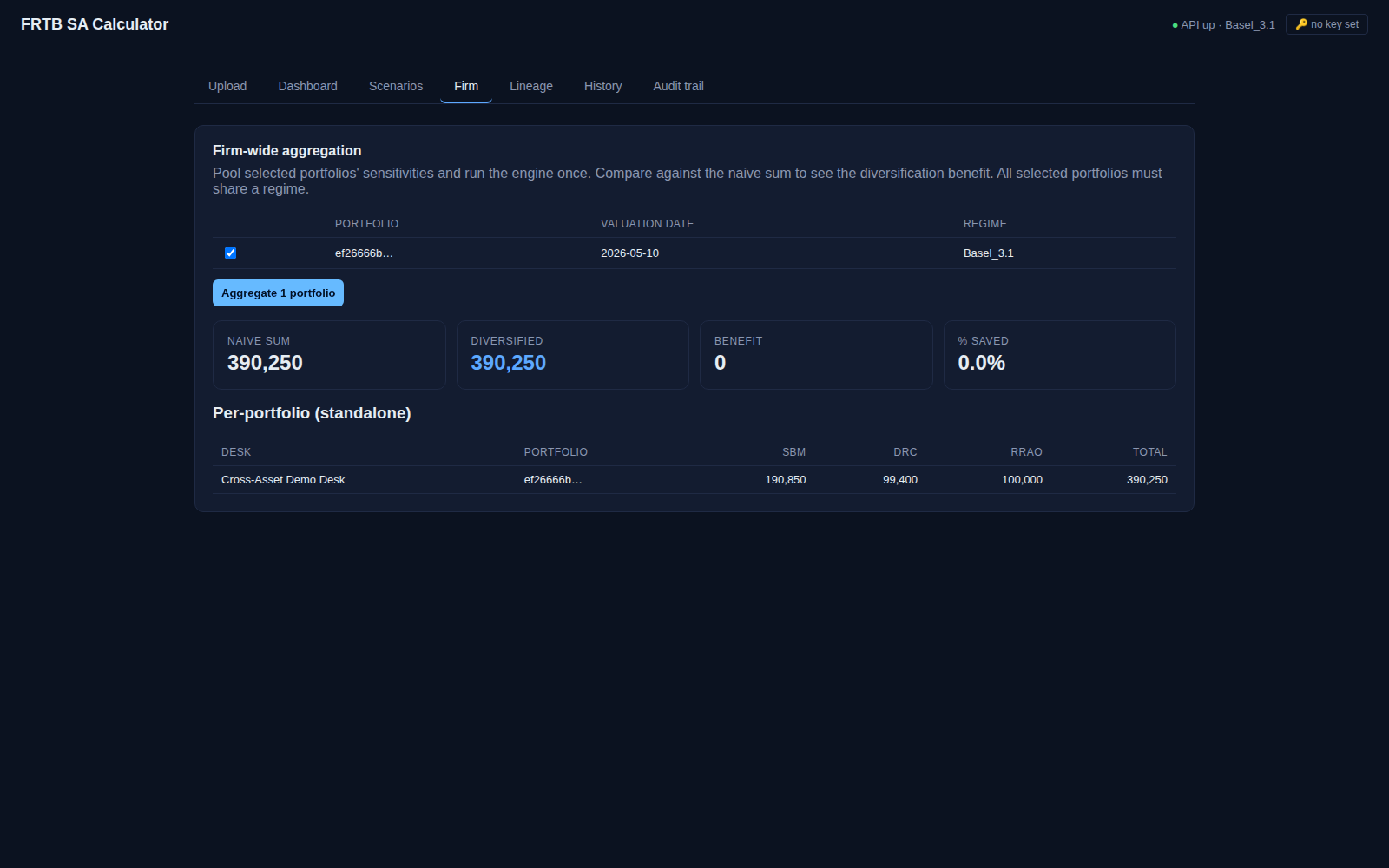
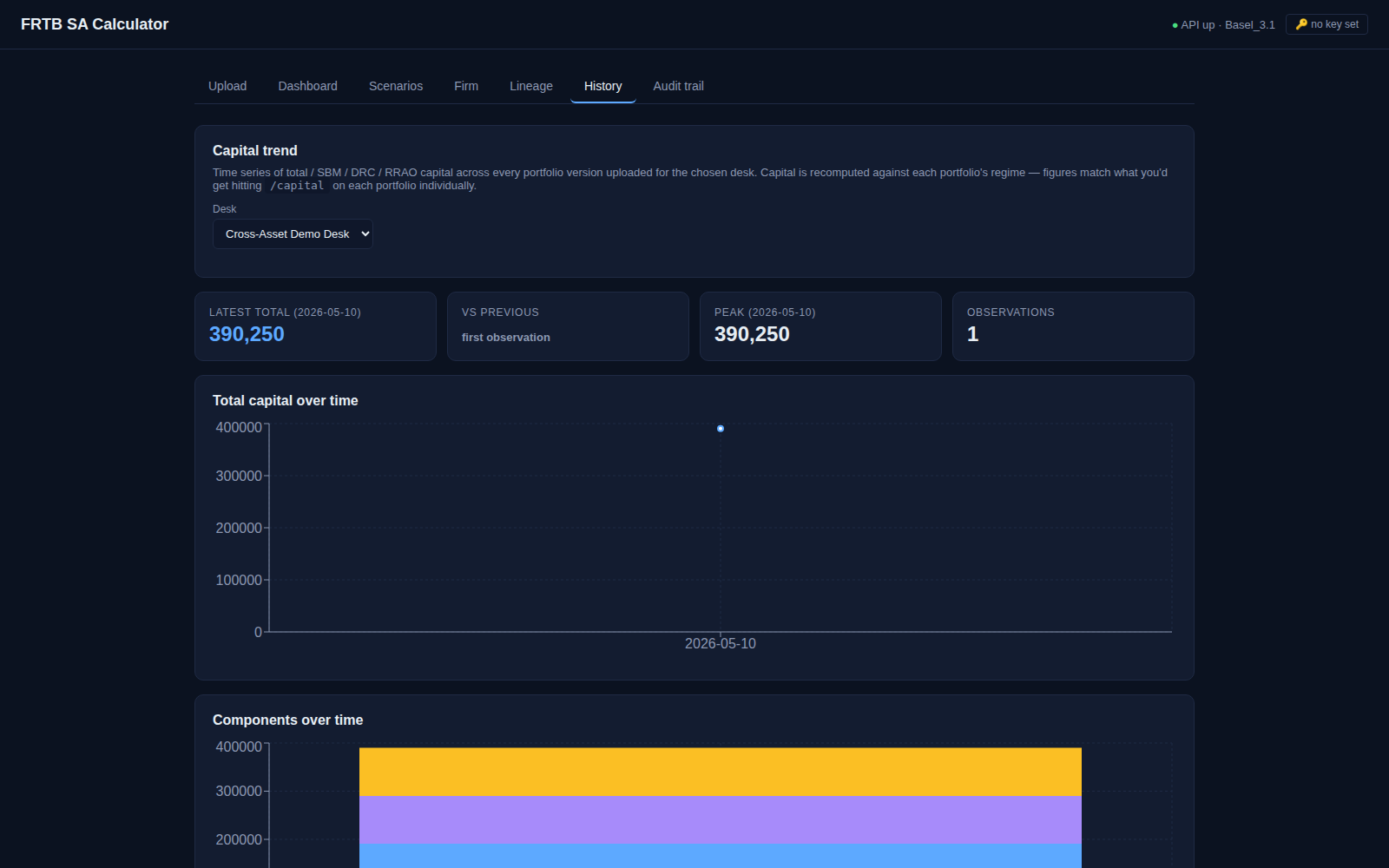
SBM · DRC · RRAO
Standardised Approach engine
IMCC + SES
Internal Models · RFET / NMRF
PRA · EBA · APRA
Regulator-template exports